Long-lived secrets have a bad habit of surviving every architecture review. Teams know they should reduce them, but delivery pressure keeps pushing the cleanup to later. Then an AI workflow shows up with prompt orchestration, retrieval calls, evaluation jobs, scheduled pipelines, and a few internal helpers, and suddenly the old credential sprawl problem gets bigger instead of smaller.
Microsoft Entra workload identities are one of the more practical ways to break that pattern in Azure. They let teams exchange trust signals for tokens instead of copying static secrets across CI pipelines, container apps, and automation jobs. That is useful, but it is not automatically safe. Federation reduces one class of risk while exposing design mistakes in scope, ownership, and lifecycle control.
Why AI Platforms Magnify the Secret Problem
Traditional applications often have a small set of service-to-service credentials that stay hidden behind a few stable components. Internal AI platforms are messier. A single product may touch model endpoints, search indexes, storage accounts, observability pipelines, background job runners, and external orchestration layers. If every one of those paths relies on copied client secrets, the platform quietly becomes a secret distribution exercise.
That sprawl does not only increase rotation work. It also makes ownership harder to see. When several environments share the same app registration or when multiple jobs inherit one broad credential, nobody can answer a basic governance question quickly: which workload is actually allowed to do what? By the time that question matters during an incident or audit, the cleanup is already expensive.
What Workload Identities Improve, and What They Do Not
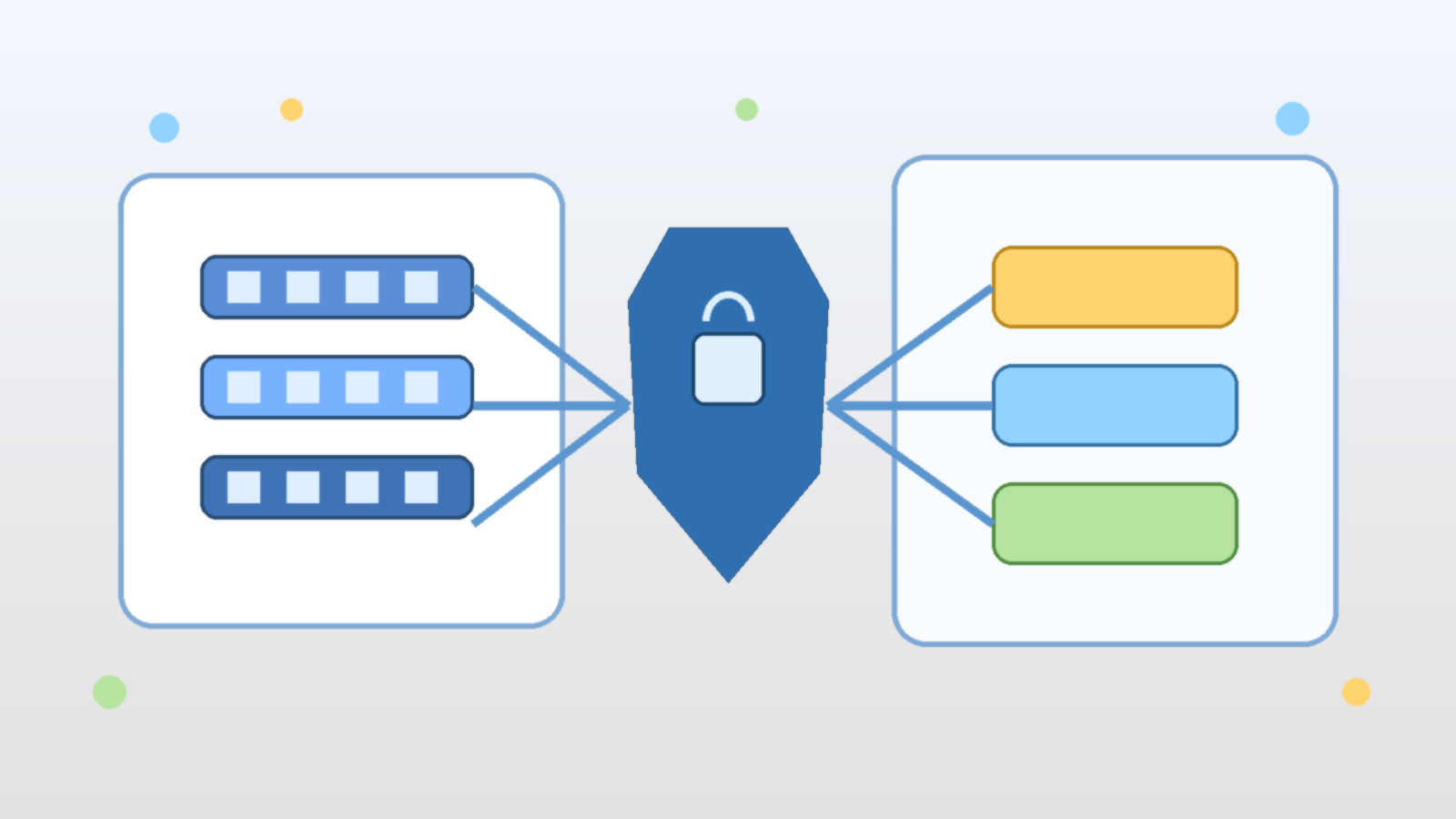
Workload identities improve the authentication path by replacing many static secrets with token exchange based on a trusted workload context. In practice, that usually means a pipeline, Kubernetes service account, containerized job, or cloud runtime proves what it is, receives a token, and uses that token to access the specific Azure resource it needs. The obvious win is that fewer long-lived credentials are left sitting in variables, config files, and build systems.
The less obvious point is that workload identities do not solve bad authorization design. If a federated workload still gets broad rights across multiple subscriptions, resource groups, or data stores, the secretless pattern only makes that overreach easier to operate. Teams should treat federation as the front door and RBAC as the real boundary. One without the other is incomplete.
Scope Each Trust Relationship to a Real Workload Boundary
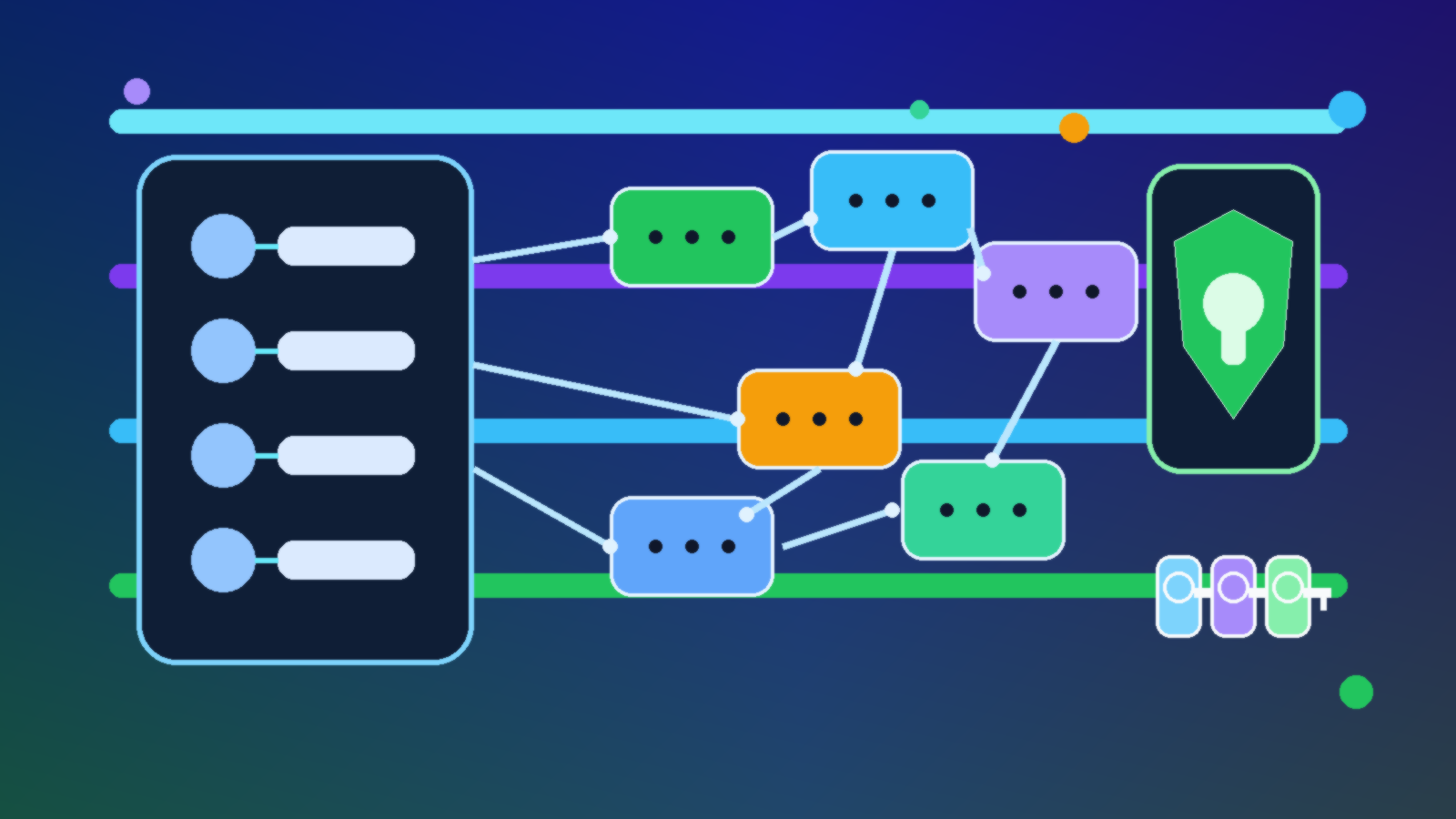
The most common design mistake is creating one flexible identity that many workloads can share. It feels efficient at first, especially when several jobs are managed by the same team. It is also how platforms drift into a world where staging, production, batch jobs, and evaluation tools all inherit the same permissions because the identity already exists.
A better pattern is to scope trust relationships to real operational boundaries. Separate identities by environment, by application purpose, and by risk profile. A retrieval indexer does not need the same permissions as a deployment pipeline. A nightly evaluation run does not need the same access path as a customer-facing inference service. If two workloads would trigger different incident responses, they probably deserve different identities.
Keep Azure AI Access Narrow and Intelligible
Azure AI projects often connect several services at once, which makes permission creep easy to miss. A team starts by granting access to the model endpoint, then adds storage for prompt assets, then adds search, then logging, then a build pipeline that needs deployment rights. None of those changes feels dramatic on its own. Taken together, they can turn one workload identity into an all-access pass.
The practical fix is boring in the best possible way. Give each workload the minimum rights needed for the resources it actually touches, and review that access when the architecture changes. If an inference app only needs to call a model endpoint and read from one index, it should not also hold broad write access to storage accounts or deployment configuration. Teams move faster when permissions make sense at a glance.
Federation Needs Lifecycle Rules, Not Just Setup Instructions
Some teams celebrate once the first federated credential works and then never revisit it. That is how stale trust relationships pile up. Repositories get renamed, pipelines change ownership, clusters are rebuilt, and internal AI prototypes quietly become semi-permanent workloads. If nobody reviews the federated credential inventory, the organization ends up with fewer secrets but a growing trust surface.
Lifecycle controls matter here. Teams should know who owns each federated credential, what workload it serves, what environment it belongs to, and when it should be reviewed or removed. If a project is decommissioned, the trust relationship should disappear with it. Workload identity is cleaner than secret sprawl, but only if dead paths are actually removed.
Logging Should Support Investigation Without Recreating Secret Chaos
One benefit of workload identities is cleaner operational evidence. Authentication events can be tied to actual workloads instead of ambiguous reused credentials. That makes investigations faster when teams want to confirm which pipeline deployed a change or which scheduled job called a protected resource. For AI platforms, that clarity matters because background jobs and agent-style workflows often execute on behalf of systems rather than named humans.
The trick is to preserve useful audit signals without turning logs into another dumping ground for sensitive detail. Teams usually need identity names, timestamps, target resources, and outcomes. They do not need every trace stream to become a verbose copy of internal prompt flow metadata. The goal is enough evidence to investigate and improve, not enough noise to hide the answer.
Migration Works Better When You Target the Messiest Paths First
Trying to replace every static secret in one motion usually creates friction. A better approach is to start where the pain is obvious. Pipelines with manual secret rotation, shared nonhuman accounts, container jobs that inherit copied credentials, and AI automation layers with too many environment variables are strong candidates. Those paths tend to deliver security and operational wins quickly.
That sequencing also helps teams learn the pattern before they apply it everywhere. Once ownership, RBAC scope, review cadence, and monitoring are working for the first few workloads, the rollout becomes easier to repeat. Secretless identity is most successful when it becomes a platform habit instead of a heroic migration project.
Final Takeaway
Microsoft Entra workload identities are one of the cleanest ways to reduce credential sprawl in Azure AI environments, but they are not a shortcut around governance. The value comes from matching each trust relationship to a real workload boundary, keeping RBAC narrow, and cleaning up old paths before they fossilize into permanent platform debt.
Teams that make that shift usually get two wins at once. They reduce the number of secrets lying around, and they get a clearer map of what each workload is actually allowed to do. In practice, that clarity is often worth as much as the security improvement.