When an engineering team decides to add a large language model to their product, one of the first architectural forks in the road is whether to route through Azure OpenAI Service or connect directly to the OpenAI API. Both surfaces expose many of the same models. Both let you call GPT-4o, embeddings endpoints, and the assistants API. But the governance story, cost structure, compliance posture, and operational experience are meaningfully different — and picking the wrong one for your context creates technical debt that compounds over time.
This guide walks through the real decision criteria so you can make an informed call rather than defaulting to whichever option you set up fastest in a proof of concept.
Why the Two Options Exist at All
OpenAI publishes a public API that anyone with a billing account can use. Azure OpenAI Service is a licensed deployment of the same model weights running inside Microsoft’s cloud infrastructure. Microsoft and OpenAI have a deep partnership, but the two products are separate products with separate SKUs, separate support contracts, and separate compliance certifications.
The existence of both is not an accident. Enterprise buyers often have Microsoft Enterprise Agreements, data residency requirements, or compliance mandates that make the Azure path necessary regardless of preference. Startups and smaller teams often have the opposite situation: they want the fastest path to production with no Azure dependency, and the OpenAI API gives them that.
Data Privacy and Compliance: The Biggest Differentiator
For many organizations, this section alone determines the answer. Azure OpenAI Service is covered by the Microsoft Azure compliance framework, which includes SOC 2, ISO 27001, HIPAA Business Associate Agreements, FedRAMP High (for government deployments), and regional data residency options across Azure regions. Customer data processed through Azure OpenAI is not used to train Microsoft or OpenAI models by default, and Microsoft’s data processing agreements with enterprise customers give legal teams something concrete to review.
The public OpenAI API has its own privacy commitments and an enterprise tier with stronger data handling terms. For companies that are already all-in on Microsoft’s compliance umbrella, however, Azure OpenAI fits more naturally into existing audit evidence and vendor management processes. If your legal team already trusts Azure for sensitive workloads, adding an OpenAI API dependency creates a second vendor to review, a second DPA to negotiate, and a second line item in your annual vendor risk assessment.
If your workload involves healthcare data, government information, or anything subject to strict data localization requirements, Azure OpenAI Service is usually the faster path to a compliant architecture.
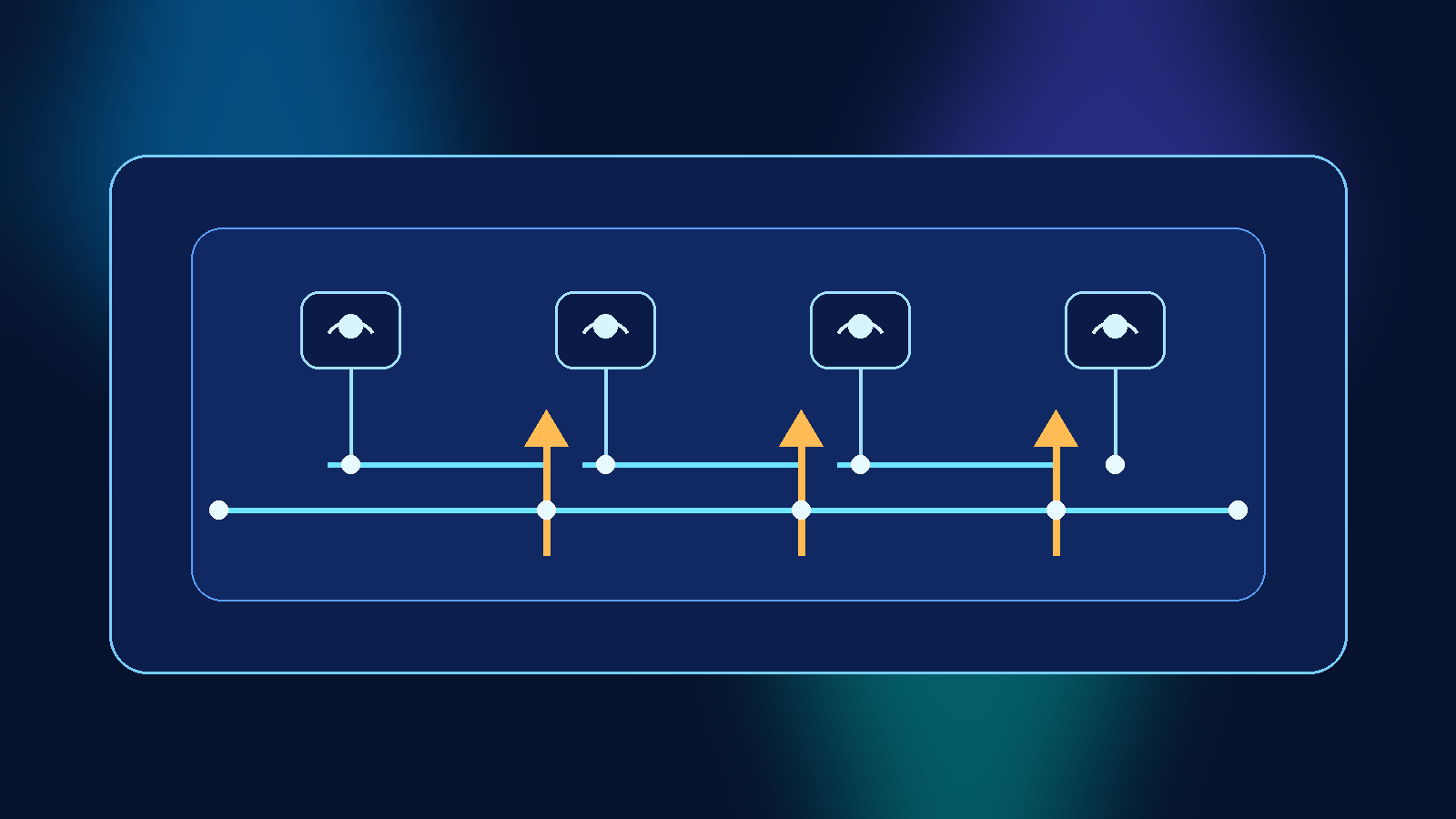
Model Availability and the Freshness Gap
This is where the OpenAI API often has a visible advantage: new models typically appear on the public API first, and Azure OpenAI gets them on a rolling deployment schedule that can lag by weeks or months depending on the model and region. If you need access to the absolute latest model version the day it launches, the OpenAI API is the faster path.
For most production workloads, this freshness gap matters less than it seems. If your application is built against GPT-4o and that model is stable, a few weeks between OpenAI API availability and Azure OpenAI availability is rarely a blocker. Where it does matter is in research contexts, competitive intelligence use cases, or when a specific new capability (like an expanded context window or a new modality) is central to your product roadmap.
Azure OpenAI also requires you to provision deployments in specific regions and with specific capacity quotas, which can create lead time before you can actually call a new model at scale. The public OpenAI API shares capacity across a global pool and does not require pre-provisioning in the same way, which makes it more immediately flexible during prototyping and early scaling stages.
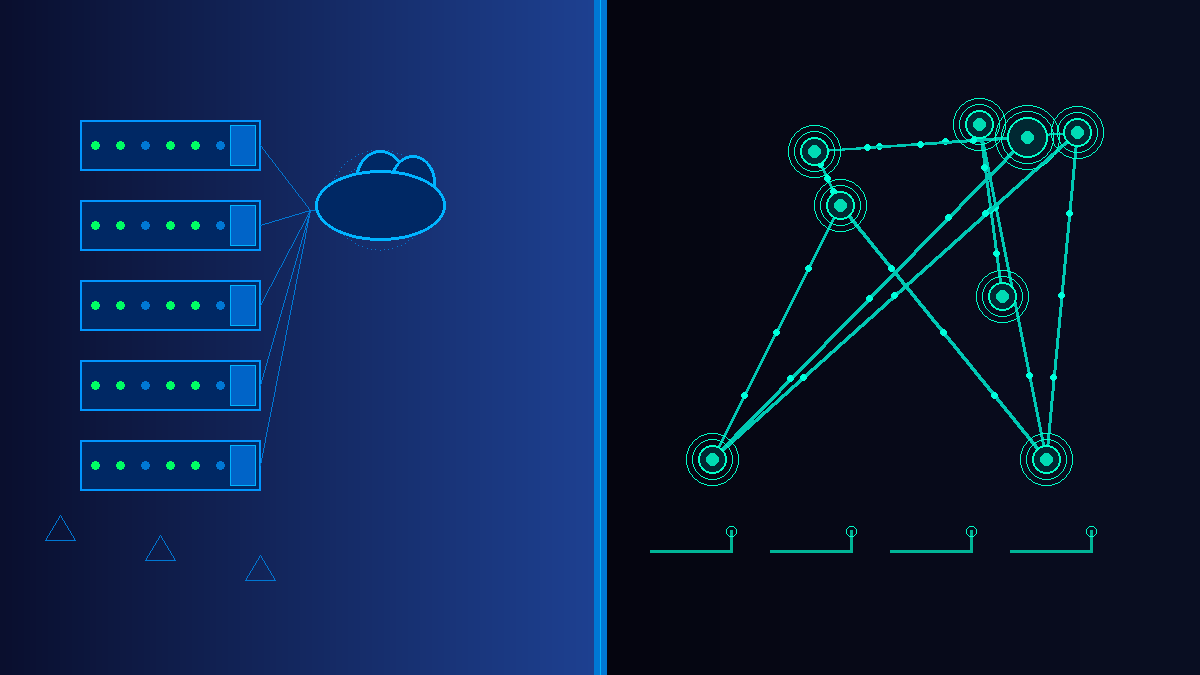
Networking, Virtual Networks, and Private Connectivity
If your application runs inside an Azure Virtual Network and you need your AI traffic to stay on the Microsoft backbone without leaving the Azure network boundary, Azure OpenAI Service supports private endpoints and VNet integration directly. You can lock down your Azure OpenAI resource so it is only accessible from within your VNet, which is a meaningful control for organizations with strict network egress policies.
The public OpenAI API is accessed over the public internet. You can add egress filtering, proxy layers, and API gateways on top of it, but you cannot natively terminate the connection inside a private network the way Azure Private Link enables for Azure services. For teams running zero-trust architectures or airgapped segments, this difference is not trivial.
Pricing: Similar Models, Different Billing Mechanics
Token pricing for equivalent models is generally comparable between the two platforms, but the billing mechanics differ in ways that affect cost predictability. Azure OpenAI offers Provisioned Throughput Units (PTUs), which let you reserve dedicated model capacity in exchange for a predictable hourly rate. This makes sense for workloads with consistent, high-volume traffic because you avoid the variable cost exposure of pay-per-token pricing at scale.
The public OpenAI API does not have a direct PTU equivalent, though OpenAI has introduced reserved capacity options for enterprise customers. For most standard deployments, you pay per token consumed with standard rate limits. Both platforms offer usage-based pricing that scales with consumption, but Azure PTUs give finance teams a more predictable line item when the workload is stable and well-understood.
If you are already running Azure workloads and have committed spend through a Microsoft Azure consumption agreement, Azure OpenAI costs can often count toward those commitments, which may matter for your purchasing structure.
Content Filtering and Policy Controls
Both platforms include content filtering by default, but Azure OpenAI gives enterprise customers more configuration flexibility over filtering layers, including the ability to request custom content policy configurations for specific approved use cases. This matters for industries like law, medicine, or security research, where the default content filters may be too restrictive for legitimate professional applications.
These configurations require working directly with Microsoft and going through a review process, which adds friction. But the ability to have a supported, documented policy exception is often preferable to building custom filtering layers on top of a more restrictive default configuration.
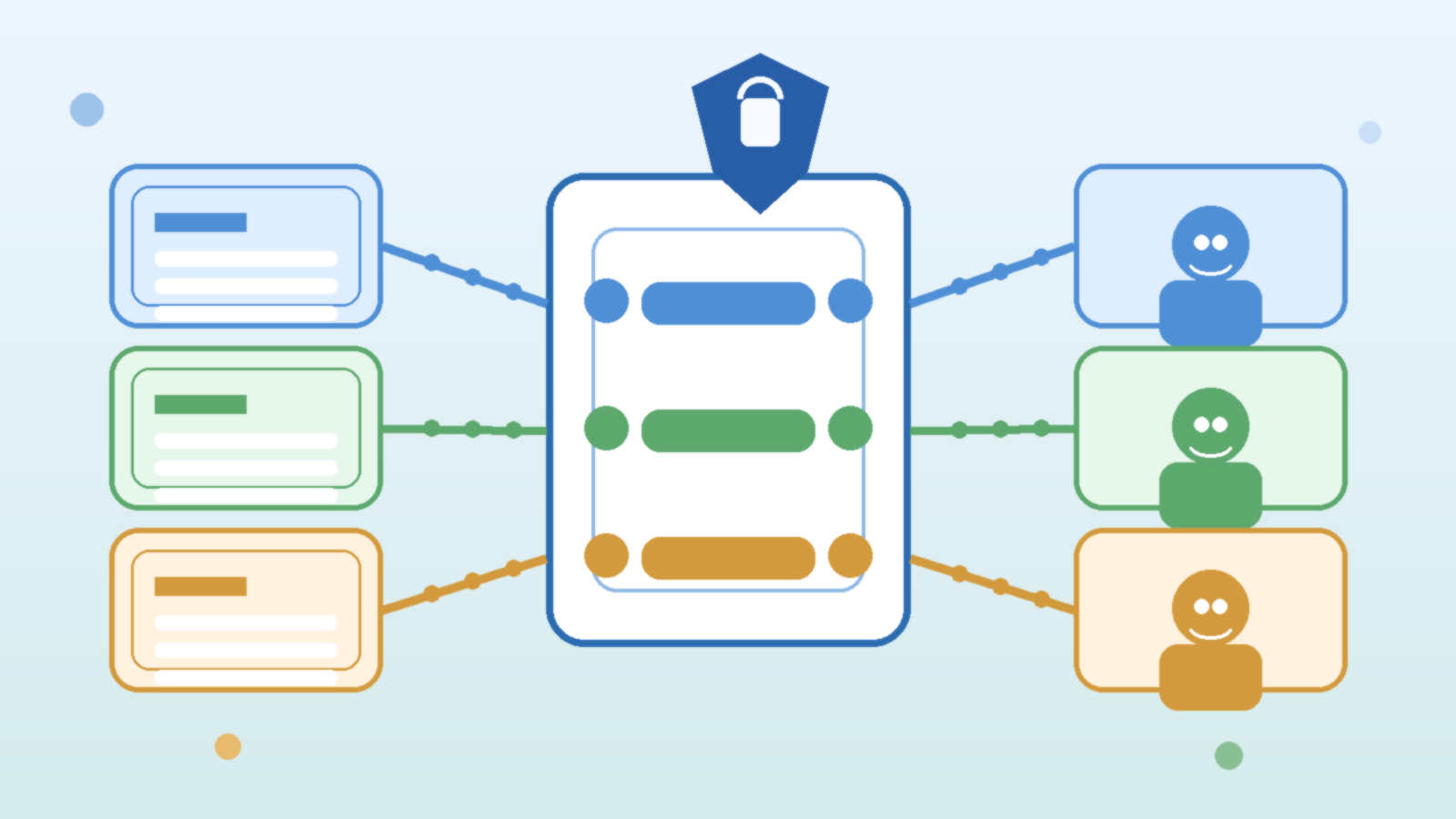
Integration with Azure Services
If your AI application is part of a broader Azure-native stack, Azure OpenAI Service integrates naturally with the surrounding ecosystem. Azure AI Search (formerly Cognitive Search) connects directly for retrieval-augmented generation pipelines. Azure Managed Identity handles authentication without embedding API keys in application configuration. Azure Monitor and Application Insights collect telemetry alongside your other Azure workloads. Azure API Management can sit in front of your Azure OpenAI deployment for rate limiting, logging, and policy enforcement.
The public OpenAI API works with all of these things too, but you are wiring them together manually rather than using native integrations. For teams who have already invested in Azure’s operational tooling, the Azure OpenAI path produces less integration code and fewer moving parts to maintain.
When the OpenAI API Is the Right Call
There are real scenarios where connecting directly to the OpenAI API is the better choice. If your company has no significant Azure footprint and no compliance requirements that push you toward Microsoft’s certification umbrella, adding Azure just to access OpenAI models adds operational overhead with no payoff. You now have another cloud account to manage, another identity layer to maintain, and another billing relationship to track.
Startups moving fast in early-stage product development often benefit from the OpenAI API’s simplicity. You create an account, get an API key, and start building. The latency to first working prototype is lower when you are not provisioning Azure resources, configuring resource groups, or waiting for quota approvals in specific regions.
The OpenAI API also gives you access to features and endpoints that sometimes appear in OpenAI’s product before they are available through Azure. If your competitive advantage depends on using the latest model capabilities as soon as they ship, the direct API path keeps that option open.
Making the Decision: A Practical Framework
Rather than defaulting to one or the other, run through these questions before committing to an architecture:
- Does your workload handle regulated data? If yes and you are already in Azure, Azure OpenAI is almost always the right answer.
- Do you have an existing Azure footprint? If you already manage Azure resources, Azure OpenAI fits naturally into your operational model with minimal additional overhead.
- Do you need private network access to the model endpoint? Azure OpenAI supports Private Link. The public OpenAI API does not.
- Do you need the absolute latest model the day it launches? The public OpenAI API tends to get new models first.
- Is cost predictability important at scale? Azure Provisioned Throughput Units give you a stable hourly cost model for high-volume workloads.
- Are you building a fast prototype with no Azure dependencies? The public OpenAI API gets you started with less setup friction.
For most enterprise teams with existing Azure commitments, Azure OpenAI Service is the more defensible choice. It fits into existing compliance frameworks, supports private networking, integrates with managed identity and Azure Monitor, and gives procurement teams a single vendor relationship. The tradeoff is some lag on new model availability and more initial setup compared to grabbing an API key and calling it directly.
For independent developers, startups without Azure infrastructure, or teams that need the newest model capabilities immediately, the OpenAI API remains the faster and more flexible path.
Neither answer is permanent. Many organizations start with the public OpenAI API for rapid prototyping and migrate to Azure OpenAI Service once the use case is validated, compliance review is initiated, and production-scale infrastructure planning begins. What matters is that you make the switch deliberately, with your architectural requirements driving the decision — not convenience at the moment you set up your first proof of concept.