Containerization changed how teams build and ship software. But choosing how to run those containers is a decision that has major downstream effects on your team's operational overhead, cost structure, and architectural flexibility. Two options that come up most often in Azure environments are Azure Kubernetes Service (AKS) and Azure Container Apps (ACA). They both run containers. They both scale. And they both sit in Azure. So what actually separates them — and when does each one win?
This post breaks down the key differences so you can make a clear, informed choice rather than defaulting to “just use Kubernetes” because it's familiar.
What Each Platform Actually Is
Azure Kubernetes Service (AKS) is Microsoft's managed Kubernetes offering. You still manage node pools, configure networking, handle storage classes, set up ingress controllers, and reason about cluster capacity. Azure handles the Kubernetes control plane, but everything from the node level down is on you. AKS gives you the full Kubernetes API — every knob, every operator, every custom resource definition.
Azure Container Apps (ACA) is a fully managed, serverless container platform. Under the hood it runs on Kubernetes and KEDA (the Kubernetes-based event-driven autoscaler), but that entire layer is completely hidden from you. You deploy containers. You define scale rules. Azure takes care of everything else, including zero-scale when traffic drops to nothing.
The simplest mental model: AKS is infrastructure you control; ACA is a platform that controls itself.
Operational Complexity: The Real Cost of Kubernetes
Kubernetes is powerful, but it does not manage itself. On AKS, someone on your team needs to own the cluster. That means patching node pools when new Kubernetes versions drop, right-sizing VM SKUs, configuring cluster autoscaler settings, setting up an ingress controller (NGINX, Application Gateway Ingress Controller, or another option), managing Persistent Volume Claims for stateful workloads, and wiring up monitoring with Azure Monitor or Prometheus.
None of this is particularly hard if you have a dedicated platform or DevOps team. But for a team of five developers shipping a SaaS product, this is real overhead that competes with feature work. A misconfigured cluster autoscaler during a traffic spike does not just cause degraded performance — it can cascade into an outage.
Azure Container Apps removes this entire layer. There are no nodes to patch, no ingress controllers to configure, no cluster autoscaler to tune. You push a container image, configure environment variables and scale rules, and the platform handles the rest. For teams without dedicated infrastructure engineers, this is a significant productivity multiplier.
Scaling Behavior: When ACA's Serverless Model Shines
Azure Container Apps was built from the ground up around event-driven autoscaling via KEDA. Out of the box, ACA can scale your containers based on HTTP traffic, CPU, memory, Azure Service Bus queue depth, Azure Event Hub consumer lag, or any custom metric KEDA supports. More importantly, it can scale all the way to zero replicas when there is nothing to process — and you pay nothing while scaled to zero.
This makes ACA an excellent fit for workloads with bursty or unpredictable traffic patterns: background job processors, webhook handlers, batch pipelines, internal APIs that see low-to-moderate traffic. If your workload sits idle for hours at a time, the cost savings from zero-scale can be substantial.
AKS supports horizontal pod autoscaling and KEDA as an add-on, but scaling to zero requires additional configuration, and you still pay for the underlying nodes even if no pods are scheduled on them (unless you are also using Virtual Nodes or node pool autoscaling all the way down to zero, which adds more complexity). For baseline-heavy workloads that always run, AKS's fixed node cost is predictable and can be cheaper than per-request ACA billing at high sustained loads.
Networking and Ingress: AKS Wins on Flexibility
If your architecture involves complex networking requirements — internal load balancers, custom ingress routing rules, mutual TLS between services, integration with existing Azure Application Gateway or Azure Front Door configurations, or network policies enforced at the pod level — AKS gives you the surface area to configure all of it precisely.
Azure Container Apps provides built-in ingress with HTTPS termination, traffic splitting for blue/green and canary deployments, and Dapr integration for service-to-service communication. For many teams, that is more than enough. But if you need to bolt Container Apps into an existing hub-and-spoke network topology with specific NSG rules and UDRs, you will find the abstraction starts to fight you. ACA supports VNet integration, but the configuration surface is much smaller than what AKS exposes.
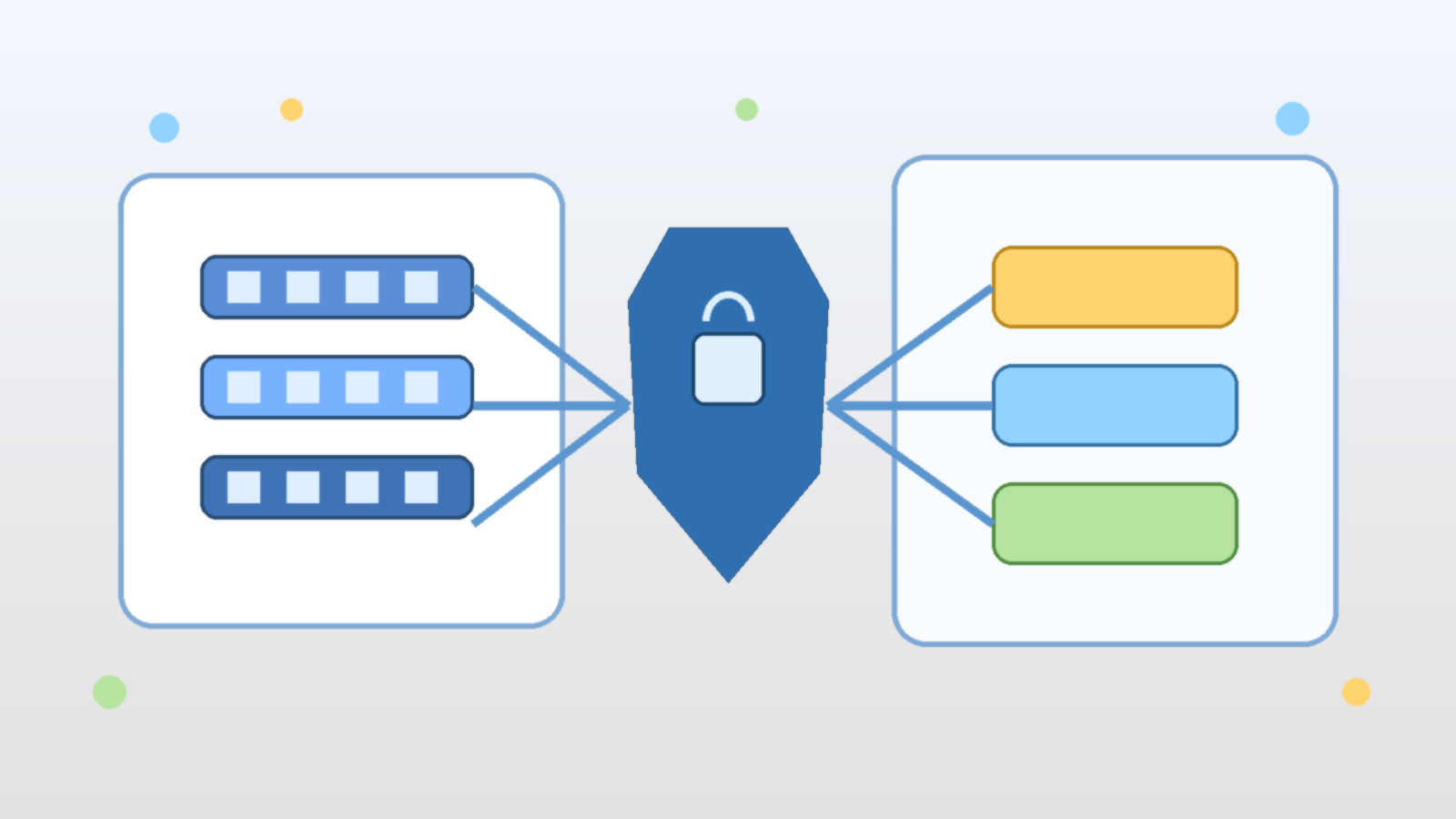
Multi-Container Architectures and Microservices
Both platforms support multi-container deployments, but they model them differently. AKS uses Kubernetes Pods, which can contain multiple containers sharing a network namespace and storage volumes. This is the standard pattern for sidecar containers — log shippers, service mesh proxies, init containers for secret injection.
Azure Container Apps supports multi-container configurations within an environment, and it has first-class support for Dapr as a sidecar abstraction. If you are building microservices that need service discovery, distributed tracing, and pub/sub messaging without wiring it all up manually, Dapr on ACA is genuinely elegant. The trade-off is that you are adopting Dapr's abstraction model, which may or may not align with how your team already thinks about inter-service communication.
For teams building a large microservices estate with diverse inter-service communication requirements, AKS with a service mesh like Istio or Linkerd still offers the most control. For teams building five to fifteen services that need to talk to each other, ACA with Dapr is often simpler to operate at any given point in the lifecycle.
Cost Considerations
Cost is one of the most common decision drivers, and neither platform is universally cheaper. The comparison depends heavily on your workload profile:
- Low or bursty traffic: ACA's scale-to-zero capability means you pay only for active compute. An API that handles 50 requests per hour costs nearly nothing on ACA. The same workload on AKS requires at least one running node regardless of traffic.
- High, sustained throughput: AKS with right-sized reserved instances or spot node pools can be significantly cheaper than ACA per-vCPU-hour at high sustained load. ACA's consumption pricing adds up when you are running hundreds of thousands of requests continuously.
- Operational cost: Do not forget the engineering time needed to manage AKS. Even at a conservative estimate of a few hours per week per cluster, that is a real cost that does not show up in the Azure bill.
When to Choose AKS
AKS is the right choice when your requirements push beyond what a managed platform can abstract cleanly. Choose AKS when you have a dedicated platform or DevOps team that can own the cluster, when you need custom Kubernetes operators or CRDs that do not exist as managed services, when your workload has complex stateful requirements with specific storage class needs, when you need precise control over networking at the pod and node level, or when you are running multiple teams with very different workloads that benefit from a shared cluster with namespace isolation and RBAC at scale.
AKS is also the better choice if your organization has existing Kubernetes expertise and well-established GitOps workflows using tools like Flux or ArgoCD. The investment in that expertise has a higher return on a full Kubernetes environment than on a platform that abstracts it away.
When to Choose Azure Container Apps
Azure Container Apps wins when developer productivity and operational simplicity are the primary constraints. Choose ACA when your team does not have or does not want to staff dedicated Kubernetes expertise, when your workloads are event-driven or have variable traffic patterns that benefit from scale-to-zero, when you want built-in Dapr support for microservice communication without managing a service mesh, when you need fast time-to-production without cluster provisioning and configuration overhead, or when you are running internal tooling, staging environments, or background processors where operational complexity would be disproportionate to the workload value.
ACA has also matured significantly since its initial release. Dedicated plan pricing, GPU support, and improved VNet integration have addressed many of the early limitations that pushed teams toward AKS by default. It is worth re-evaluating ACA even if you dismissed it a year or two ago.
The Decision in One Question
If you could only ask one question to guide this decision, ask this: Does your team want to operate a container platform, or use one?
AKS is for teams that want — or need — to operate a platform. ACA is for teams that want to use one. Both are excellent tools. Neither is the wrong answer in the right context. The mistake is defaulting to one without honestly evaluating what your specific team, workload, and organizational constraints actually need.