Prompt caching is easy to like because the benefits show up quickly. Responses can get faster, repeated workloads can get cheaper, and platform teams finally have one optimization that feels more concrete than another round of prompt tweaking. The danger is that some teams treat caching like a harmless switch instead of a policy decision.
That mindset usually works until multiple internal applications share models, prompts, and platform controls. Then the real questions appear. What exactly is being cached, how long should it live, who benefits from the hit rate, and what happens when yesterday’s prompt structure quietly shapes today’s production behavior? In enterprise AI, prompt caching is not just a performance feature. It is part of the operating model.
Prompt Caching Changes Cost Curves, but It Also Changes Accountability
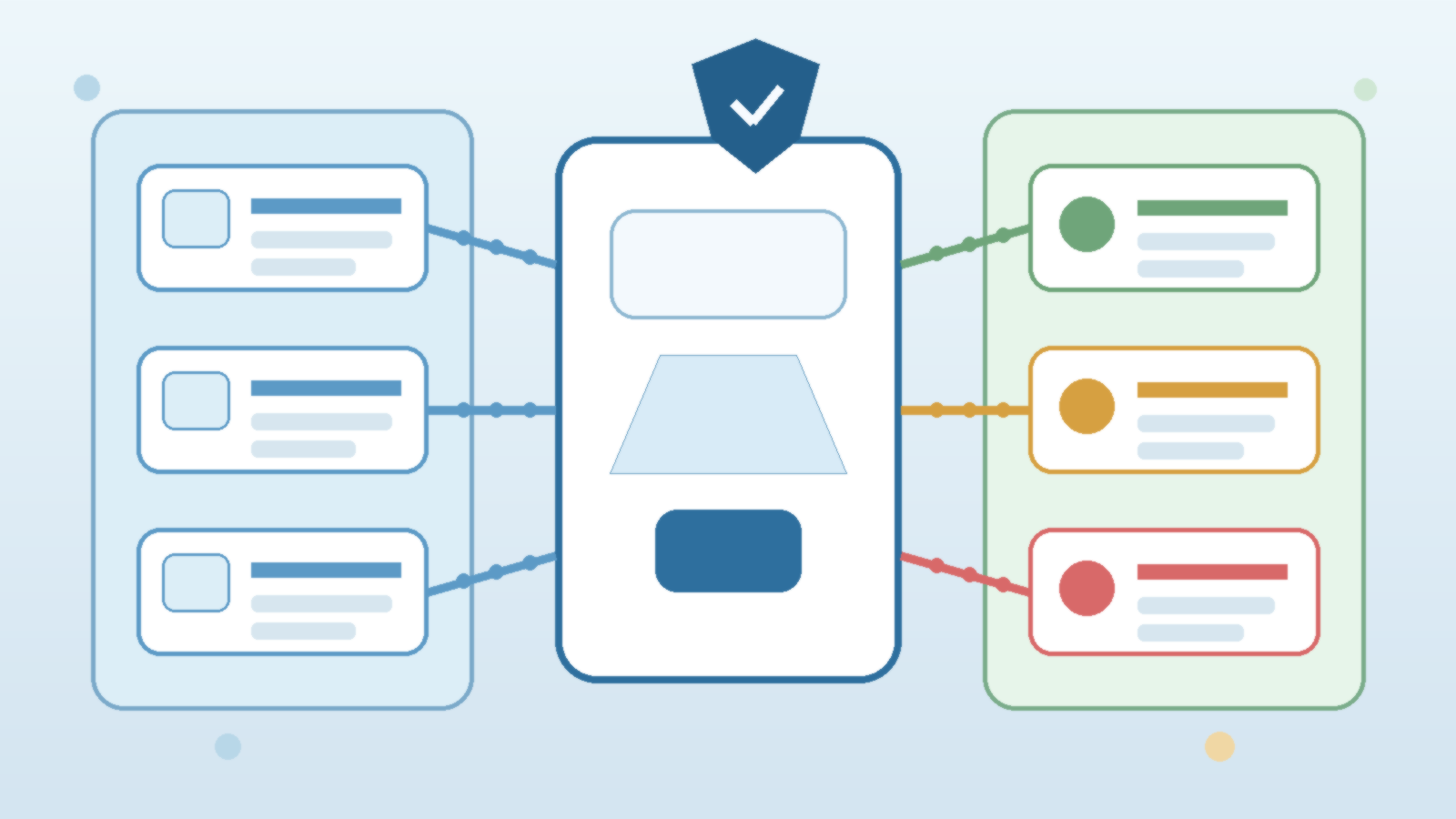
Teams often discover prompt caching during optimization work. A workflow repeats the same long system prompt, a retrieval layer sends similar scaffolding on every request, or a high-volume internal app keeps paying to rebuild the same context over and over. Caching can reduce that waste, which is useful. It can also make usage patterns harder to interpret if nobody tracks where the savings came from or which teams are effectively leaning on shared cached context.
That matters because cost visibility drives better decisions. If one group invests in cleaner prompts and another group inherits the cache efficiency without understanding it, the platform can look healthier than it really is. The optimization is real, but the attribution gets fuzzy. Enterprise teams should decide up front whether cache gains are measured per application, per environment, or as a shared platform benefit.
Cache Lifetimes Should Follow Risk, Not Just Performance Goals
Not every prompt deserves the same retention window. A stable internal assistant with carefully managed instructions may tolerate longer cache lifetimes than a fast-moving application that changes policy rules, product details, or safety guidance every few hours. If the cache window is too long, teams can end up optimizing yesterday’s assumptions. If it is too short, the platform may keep most of the complexity without gaining much efficiency.
The practical answer is to tie cache lifetime to the volatility and sensitivity of the workload. Prompts that contain policy logic, routing hints, role assumptions, or time-sensitive business rules should usually have tighter controls than generic formatting instructions. Performance is important, but stale behavior in an enterprise workflow can be more expensive than a slower request.
Shared Platforms Need Clear Boundaries Around What Can Be Reused
Prompt caching gets trickier when several teams share the same model access layer. In that setup, the main question is not only whether the cache works. It is whether the reuse boundary is appropriate. Teams should be able to answer a few boring but important questions: is the cache scoped to one application, one tenant, one environment, or a broader platform pool; can prompts containing sensitive instructions or customer-specific context ever be reused; and what metadata is logged when a cache hit occurs?
Those questions sound operational, but they are really governance questions. Reuse across the wrong boundary can create confusion about data handling, policy separation, and responsibility for downstream behavior. A cache hit should feel predictable, not mysterious.
Do Not Let Caching Hide Bad Prompt Hygiene
Caching can make a weak prompt strategy look temporarily acceptable. A long, bloated instruction set may become cheaper once repeated sections are reused, but that does not mean the prompt is well designed. Teams still need to review whether instructions are clear, whether duplicated context should be removed, and whether the application is sending information that does not belong in the request at all.
That editorial discipline matters because a cache can lock in bad habits. When a poorly structured prompt becomes cheaper, organizations may stop questioning it. Over time, the platform inherits unnecessary complexity that becomes harder to unwind because nobody wants to disturb the optimization path that made the metrics look better.
Logging and Invalidation Policies Matter More Than Teams Expect
Enterprise AI teams rarely regret having an invalidation plan. They do regret realizing too late that a prompt change, compliance update, or incident response action does not reliably flush the old behavior path. If prompt caching is enabled, someone should own the conditions that force refresh. Policy revisions, critical prompt edits, environment promotions, and security events are common candidates.
Logging should support that process without becoming a privacy problem of its own. Teams usually need enough telemetry to understand hit rates, cache scope, and operational impact. They do not necessarily need to spray full prompt contents into every downstream log sink. Good governance means retaining enough evidence to operate the system while still respecting data minimization.
Show Application Owners the Tradeoff, Not Just the Feature
Prompt caching decisions should not live only inside the platform team. Application owners need to understand what they are gaining and what they are accepting. Faster performance and lower repeated cost are attractive, but those gains come with rules about prompt stability, refresh timing, and scope. When teams understand that tradeoff, they make better design choices around release cadence, versioning, and prompt structure.
This is especially important for internal AI products that evolve quickly. A team that changes core instructions every day may still use caching, but it should do so intentionally and with realistic expectations. The point is not to say yes or no to caching in the abstract. The point is to match the policy to the workload.
Final Takeaway
Prompt caching is one of those features that looks purely technical until an enterprise tries to operate it at scale. Then it becomes a question of scope, retention, invalidation, telemetry, and cost attribution. Teams that treat it as a governed platform capability usually get better performance without losing clarity.
Teams that treat it like free magic often save money at first, then spend that savings back through stale behavior, murky ownership, and hard-to-explain platform side effects. The cache is useful. It just needs a grown-up policy around it.