Most internal AI projects start as experiments. A team wants to test a new model, compare embeddings, wire up a simple chatbot, or automate a narrow workflow. That early stage should be fast. The trouble starts when an experiment is allowed to borrow production access because it feels temporary. Temporary shortcuts tend to survive long enough to become architecture.
In Azure environments, this usually shows up as a small proof of concept that can suddenly read real storage accounts, call internal APIs, or reach production secrets through an identity that was never meant to carry that much trust. The technical mistake is easy to spot in hindsight. The organizational mistake is assuming experimentation and production can share the same access model without consequences.
Fast Experiments Need Different Defaults Than Stable Systems
Experimentation has a different purpose than production. In the early phase, teams are still learning whether a workflow is useful, whether a model choice is affordable, and whether the data even supports the outcome they want. That uncertainty means the platform should optimize for safe learning, not broad convenience.
When the same subscription, identities, and data paths are reused for both experimentation and production, people stop noticing how much trust has accumulated around a project that has not earned it yet. The experiment may still be immature, but its permissions can already be very real.
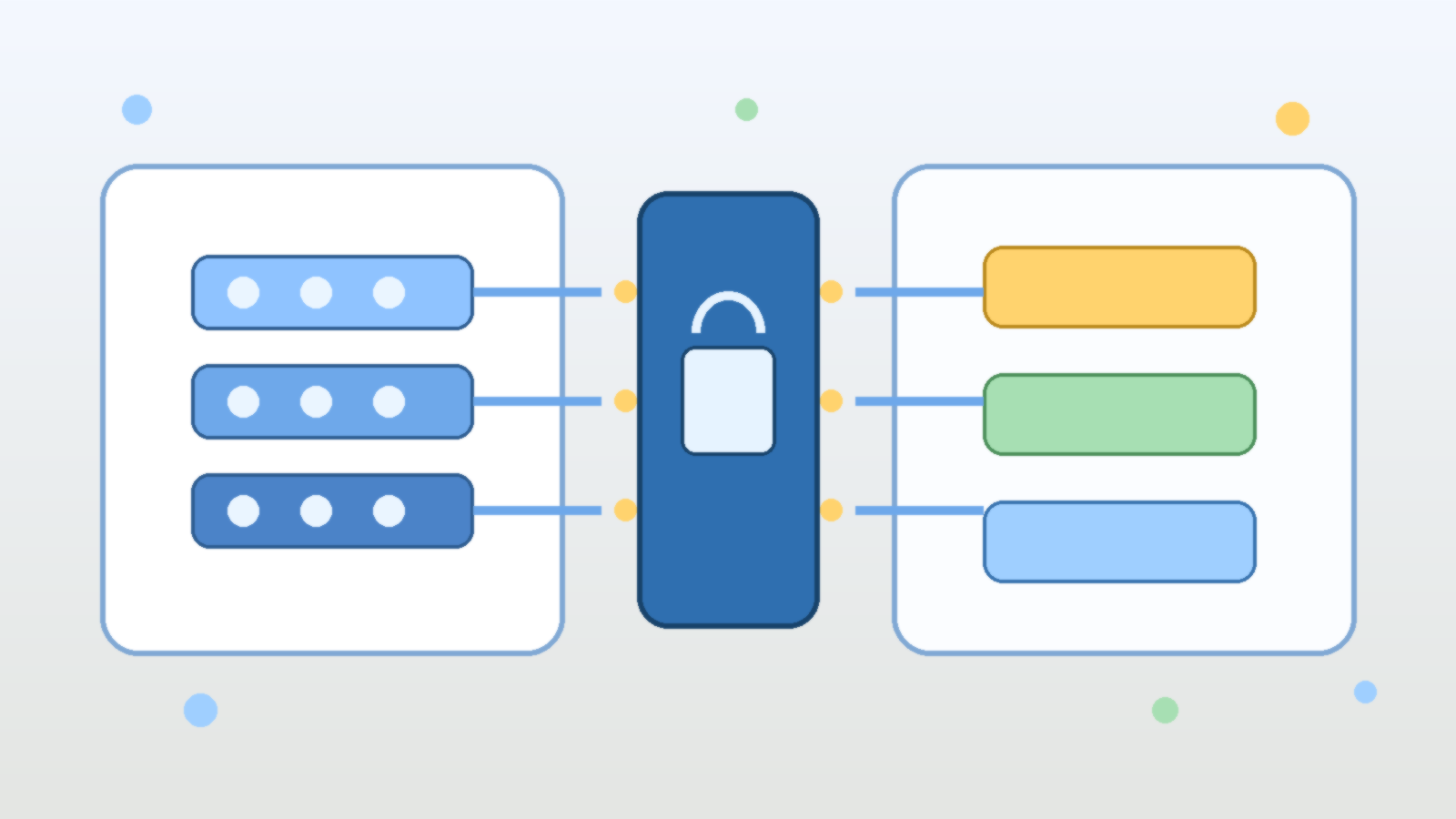
Separate Environments Are About Trust Boundaries, Not Just Cost Centers
Some teams create separate Azure environments mainly for billing or cleanup. Those are good reasons, but the stronger reason is trust isolation. A sandbox should not be able to reach production data stores just because the same engineers happen to own both spaces. It should not inherit the same managed identities, the same Key Vault permissions, or the same networking assumptions by default.
That separation makes experimentation calmer. Teams can try new prompts, orchestration patterns, and retrieval ideas without quietly increasing the blast radius of every failed test. If something leaks, misroutes, or over-collects, the problem stays inside a smaller box.
Production Data Should Arrive Late and in Narrow Form
One of the fastest ways to make a proof of concept look impressive is to feed it real production data early. That is also one of the fastest ways to create a governance mess. Internal AI teams often justify the shortcut by saying synthetic data does not capture real edge cases. Sometimes that is true, but it should lead to controlled access design, not casual exposure.
A healthier pattern is to start with synthetic or reduced datasets, then introduce tightly scoped production data only when the experiment is ready to answer a specific validation question. Even then, the data should be minimized, access should be time-bounded when possible, and the approval path should be explicit enough that someone can explain it later.
Identity Design Matters More Than Team Intentions
Good teams still create risky systems when the identity model is sloppy. In Azure, that often means a proof-of-concept app receives a role assignment at the resource-group or subscription level because it was the fastest way to make the error disappear. Nobody loves that choice, but it often survives because the project moves on and the access never gets revisited.
That is why experiments need their own identities, their own scopes, and their own role reviews. If a sandbox workflow needs to read one container or call one internal service, give it exactly that path and nothing broader. Least privilege is not a slogan here. It is the difference between a useful trial and a quiet internal backdoor.
Approval Gates Should Track Risk, Not Just Project Stage
Many organizations only introduce controls when a project is labeled production. That is too late for AI systems that may already have seen sensitive data, invoked privileged tools, or shaped operational decisions during the pilot stage. The control model should follow risk signals instead: real data, external integrations, write actions, customer impact, or elevated permissions.
Once those signals appear, the experiment should trigger stronger review. That might include architecture sign-off, security review, logging requirements, or clearer rollback plans. The point is not to smother early exploration. The point is to stop pretending that a risky prototype is harmless just because nobody renamed it yet.
Observability Should Tell You When a Sandbox Is No Longer a Sandbox
Teams need a practical way to notice when experimental systems begin to behave like production dependencies. In Azure, that can mean watching for expanding role assignments, increasing usage volume, growing numbers of downstream integrations, or repeated reliance on one proof of concept for real work. If nobody is measuring those signals, the platform cannot tell the difference between harmless exploration and shadow production.
That observability should include identity and data boundaries, not just uptime graphs. If an experimental app starts pulling from sensitive stores or invoking higher-trust services, someone should be able to see that drift before the architecture review happens after the fact.
Graduation to Production Should Be a Deliberate Rebuild, Not a Label Change
The safest production launches often come from teams that are willing to rebuild key parts of the experiment instead of promoting the original shortcut-filled version. That usually means cleaner infrastructure definitions, narrower identities, stronger network boundaries, and explicit operating procedures. It feels slower in the short term, but it prevents the organization from institutionalizing every compromise made during discovery.
An AI experiment proves an idea. A production system proves that the idea can be trusted. Those are related goals, but they are not the same deliverable.
Final Takeaway
AI experimentation should be easy to start and easy to contain. In Azure, that means separating sandbox work from production access on purpose, keeping identities narrow, introducing real data slowly, and treating promotion as a redesign step rather than a paperwork event.
If your fastest AI experiments can already touch production systems, you do not have a flexible innovation model. You have a governance debt machine with good branding.
Leave a Reply